Recent Ransomware observations, Telefonica, NHS and some tips to consider
As you may be aware, the last couple of weeks in cybersecurity have being quite interesting (for non-victims). Big discussions around how Intel have managed their most recent vulnerability, how to protect yourself from being a victim and obviously the frustration a lot of people and companies felt when they noticed there was nothing they could do to fix it! But, Intel was vanished from the scene due to the exploitation of a social engineering attack: Ransomware (WannaCryptor).
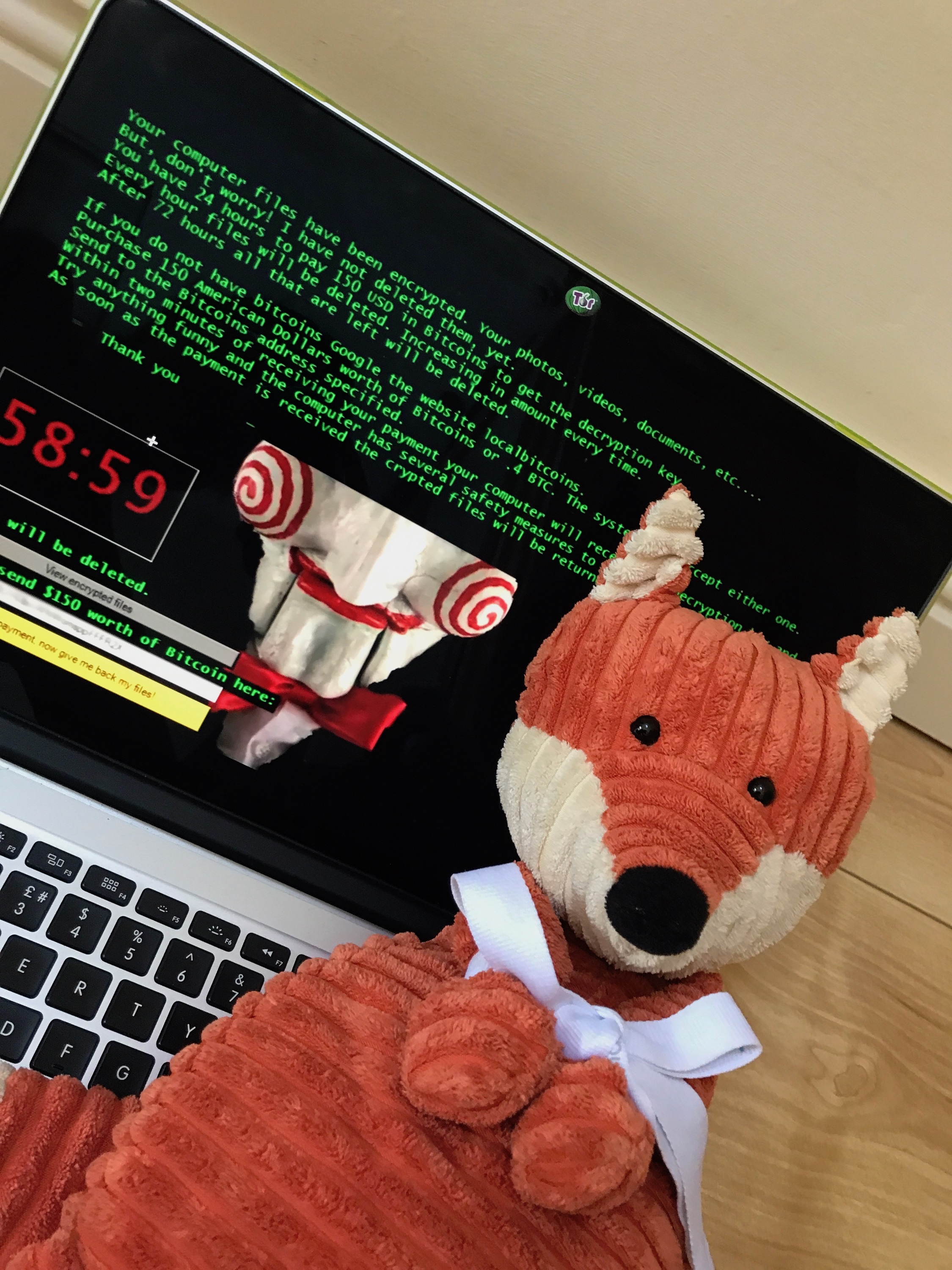
Ransomware as many of you may know is a malicious software (malware) that once it's gained a new victim, encrypts all their files and then demands a payment in order to decrypt them again. In most cases victims do not get their files back, even though they are already down hundreds or maybe thousands of dollars.
On the last 12th of May Telefonica (Spain), the NHS (UK) and some other companies/ countries were affected by a Ransomware attack. Disruption of operations and the necessity of reverting to good “old-style” (pen and paper) was the most notorious impact. To date none of the victims have made any announcement regarding data loss.
Since these events have been well covered, I'd like to share a few cybersecurity tips that might just help prevent such devastation in the future for you or the company/ organisation you work for.
Let’s start by saying that Ransomware attacks are a combination of social engineering attacks and the exploitation of a (known) vulnerability. Social engineering attacks can also be a combination of technical and social networking techniques, in which the objective is to gain someone’s trust with a view to obtaining some reward (money, information, access to something). Social engineering attacks are not something to be managed through “technical” components, instead are a combination of education, profiling, detection and prevention techniques. So, here we go:
Security awareness: Educate yourself, your family, friends, colleagues, everyone. Don’t take me wrong, but current scandals and media actions have definitely put the Ransomware’s name on everyone’s head. This is indeed, the best moment to talk about what social engineering attacks are, how much cybersecurity matters and how to protect our data (Link to my presentation and blogpost).
Do not rely on your users: No, it is not the user’s fault and you cannot rely on them. Everyone plays an important role in today’s interconnected world, and apart from knowing the basics of cybersecurity, the only ones obligated to be experts at it… are the “cybersecurity experts” (BTW, such a thing does not exist). So, if you cannot rely on security awareness programs nor trust your users; what’s next?
Software updates: Vulnerability management processes and good practices are the two winners in this category. An up-to-date system makes us somehow “immune” to known vulnerabilities. It is important to classify the likelihood vs impact of a vulnerability and prioritise them. (Telfonica's case shows how a patch released in March is still causing damage in May).
Tools and policies: Cybersecurity is not a “one-tool” solution, rather it is a combination of policies, good practices and yes, well configured tools. Below is a list of some tips and recommendations for small-medium companies and why not, home:
- Least privilege: This is not a tool, but a policy in which the purpose is to limit user’s actions to their roles, i.e. if a user does not require admin privileges, then they should not have them
- Network segregation: Depending on the size of your network, this may or may not be possible. Anyway, there are some special kinds of malware with a core purpose of spreading themselves in an exponential manner. In the case of internal networks and/ or interconnected networks, segregation is important as it may limit the malware’s area of operation
- Intrusion detection/ prevention systems (IDS/ IPS): Within this category it's possible to find signature and behavioural based IDS/ IPS. Signature-based IDS/ IPS identify intrusions (illegal actions) depending on their signatures contained within the database. Behavioural-based IDS/ IPS create a profile of a host or network, to then identify anomaly activities by comparing them with the expected normal activity. A combination of both is ideal
- Integrity checkers: Tools that allow you to identify when a file/ platform has experienced unexpected changes
- Log management: Combination of tools and processes. The idea is to collect logs from day by day tools (Word processors, browsers, etc) in order to identify unexpected behaviour. Of course, to identify these it is necessary to analyse the logs… there are many log analysis tools readily available on the Internet
- Perimeter tools (firewalls, ACLs, etc): Their main purpose is not to identify vulnerabilities, but to give you the option to apply the least privilege policy to your systems/ platforms. In other words, they sit at the perimeter of your system/ platform allowing or denying traffic depending on certain kinds of rules which should be defined according to business necessities instead of using the default settings
- Antivirus, anti-spam, anti-spyware, anti-everything: Their names speak for themselves. These kind of tools (when kept up to date) help you to identify and prevent the execution of viruses, spam messages, spyware, etc. Note: They are signature based, therefore can only identify previously identified behaviours
I hope you enjoyed reading this post.
Thanks,
eepica
Ps: Microsoft has release a guidance for WannaCrypt attacks, as well as emergency patches for obsolete systems. For more information check their website here.